Layered security provides superior protection for plant control systems
Layered security is a well-documented practice that allows an organization selectively to implement multiple layers of security technology for its plant control systems. The technology is applied according to the plant’s security policy and perceived business risk.
Layered security is a practice that involves implementing multiple security technologies in each layer of a computing system to reduce the risk of unauthorized intrusion. Exposure to intrusions increases as plant control systems migrate to open technologies such as Ethernet, Windows, and the internet protocol.
Plant operators can apply layered security by adopting a “best practices” model, developing and implementing an access-control plan, and compartmentalizing the network. At a minimum, plant networks should be compartmentalized according to business and control functions.
The plant operator can implement additional compartmentalization within a plant’s control network according to level of criticality. Personnel should be grouped by job function and used to secure a computing system further by restricting access to only the functions performed in that system.
Control systems
Plant control systems have traditionally been built with proprietary technology. This technology provided a reasonable level of security from unauthorized access due to its “closed” nature and lack of connection to business networks and the internet.
Vendors, however, are beginning to change their plant control technologies to more open networks and operating systems such as Unix, Linux, Windows, Ethernet, and the internet Protocol.
In some instances, plant control systems have access to the internet. This feature is due to a need to offer advanced graphical user interfaces to manage system components, and to integrate business and plant control networks to share point-based data with business information systems.
In parallel to this change to open systems, the US government is becoming involved in information security by creating organizations such as the Department of Homeland Security. This department is responsible for defining and enforcing security standards for critical infrastructure such as power generation, chemical production, refining, water treatment, and pipelines to protect against both external and internal intrusion.
Changing plant controls to open systems exposes all layers of the computing system to unauthorized access. A layered security model helps to increase security at each computing layer-personnel, network, operating system, application, and database.
Layering security technology in a computing system creates multiple points of resistance to intruders and helps to achieve high availability. MacLeod and Whyte refer to layered security as a strategic deployment of multiple security countermeasures to reduce the risk associated with the failure of any single technology layer. Additionally, they suggest that countermeasures used in layered security are effective when a system can better fulfill its mission with these countermeasures.1
Plant owners can implement information-security technology such as continuous examination, intrusion prevention and detection, firewalls, virtual private networks (VPN), and data encryption in each computing layer of plant control systems to maximize security and address governments’ information-security standards. At a minimum, an effective layered security model should include some form of examination, detection, and prevention in the personnel, network, and operating system layers.
Securing plant control systems
A layered security model is effective when supported with an access-control plan that identifies computing systems, functional groups, and detailed access matrices.
Compartmentalization is a technique used to segment network space to control access better and isolate risk of exposure. A variety of security products can be layered into “compartments” to address examination, detection, prevention, and encryption requirements.
Layered model
A layered security model incorporates security products and best practices in all layers of a computing system. Layered security exponentially increases the cost and difficulty of penetration for an attacker by combining different security products to create a defensive barrier much stronger than the individual components. Thus, layered security decreases the likelihood that the attacker will pursue an organization.2
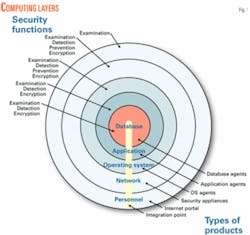
Computing systems consist of personnel, networks, operating systems, applications, and databases (Fig. 1). Information security, as a practice, focuses on securing an organization’s most important asset-its data.
Data are the basic underlying components that organizations strive to develop, store, and protect; an organization should implement a security model that focuses on providing multiple layers of resistance to these data.
There are four basic security functions that should be implemented in a complementary manner to secure each layer of a computing system: examination, detection, prevention, and encryption (Fig. 1). One can implement these security functions using a variety of security products.
Fig. 1 shows how different types of security products (i.e., security appliances, host agents) are layered into a computing system to support examination, detection, prevention, and encryption. Examining for vulnerabilities, detecting intrusions, preventing unauthorized access, and encrypting access through a network are all activities performed by these types of security products.
Access-control plan
Layering security products into plant control systems requires identifying “scope of access” for personnel, job functions, and computing systems. Detailed information related to function and accessibility to services is required for examination, detection, prevention, and encryption products to be correctly configured.
Many of these security products use rules, signatures, and policies to evaluate, detect, and accept or deny traffic through a network. A layered security model is most effective when supported by an access-control plan that addresses access from different groups (i.e., personnel, function groups, computing systems).
An effective access-control plan defines electronic access for personnel by primary job function and computing system. Additionally, such a plan can further identify access for functional groups that have secondary job functions (development vs. support).
Personnel with similar job responsibilities can be grouped by function, which supports segmentation of computing systems according to the functions performed within those systems. Security technology becomes easier to configure and maintain when computing systems can be isolated and personnel are grouped by job function within those computing systems.
Computing systems
Organizations typically have one or more computing systems to support business activities. In plant control systems, one computing system typically controls the production process, and another computing system focuses on business operations in support of production. Many plants do not separate their computing assets; rather, they implement a single system with little or no security.
A layered security model is most effective when separate computing systems can be created and functions can be isolated by system. In later-generation plant control systems, there may be multiple layers of control assets with varying levels of importance.
Typically, plant controls are deployed into a single computing system; however, a plant control system can be further separated by importance to provide an added layer of security.
Functional groups
Grouping personnel according to job function further supports a layered security model by segmenting the network space by function. Additionally, functional groups can be further controlled by the type and level of access required within each computing system.
Many organizations group personnel according to a product or service line, which increases the complexity of the security model, especially when functional groups have multiple roles (i.e., development, support) that cross product or service lines. The most effective grouping model is aligned with such job functions as accounting, database engineering, system engineering, human resources, so forth.
Identifying functional groups in plant control systems is imperative to creating a security model that protects highly critical controls. Additionally, plant control systems are typically well structured to support a functional grouping due to the separation of job responsibility by production process.
Further segmentation of plant control systems by importance can promote further segmentation of functional groups.
Access matrices
An access control plan includes a mid-level security policy and set of access matrices. Mid-level policy addresses access to basic computing services such as email, file and print services, and the internet. Access matrices provide detailed definition on scope of access within a computing system by employee and function.
Access matrices should identify accessibility to other computing systems according to functions and types of services required in those systems. Specifically, access matrices should provide a sufficient level of detail to develop firewall policies, examination rules, signatures for intrusion detection, and VPN points.
Compartmentalization
A common practice in network and security engineering is to compartmentalize network systems. Segmenting a network space into computing systems is one form of compartmentalization; however, further segmentation within a computing system is where true compartmentalization is effective.
Compartmentalization focuses on segmenting network space to support the introduction of security products such as firewalls and intrusion detection and to reduce the complexity of policies, signatures, and rule sets. Compartmentalization becomes more effective when job functions can be grouped within a compartment.
Plant control systems are typically the most critical systems in an organization; thus, critical systems should not only be isolated from business networks but also compartmentalized by level of importance.
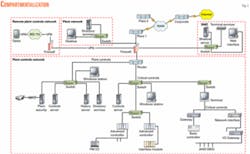
Fig. 2 shows a compartmentalization scheme that incorporates a firewall to separate plant controls, plant information technology, remote plant controls, and a demilitarized zone (see attached box for definition). This level of compartmentalization reduces the complexity of the corporate firewall policy and reduces the complexity of the plant firewall.
The plant controls network in Fig. 2 can be further segmented to enhance security between the less critical assets (plant controls) and those critical assets responsible for basic operation (critical controls). At a minimum, the plant controls and plant IT networks should be compartmentalized to protect the plant controls network from access to public networks (internet). This architecture allows the plant IT network to access business services such as email, accounting, and the internet without compromising security in the plant controls network.
This level of compartmentalization further promotes the use of intrusion prevention, intrusion detection, and examination within each network; thus creating a layered security structure.
Implementation
A layered security model advocates the use of security products at all computing layers; however, there are four basic classes of security products that should be part of any layered security architecture: examination, detection, prevention, and encryption.
Examination products typically focus on vulnerability analysis, hardening, and tuning of computing assets. Detection products focus on identifying intrusions once they are inside the computing system.
Prevention products focus on preventing unauthorized access to specific networks and hosts according to a predefined policy. Encryption products focus on securing data during transmission and storage.
Although there are many other types of security products used in business, these four classes of security products should serve as the foundation for an effective security policy.
Examination
Examination products are commonly referred to as “scanning” technologies. Examination is a technique used to identify vulnerabilities in all computing layers before they become compromised.
Examination at the personnel layer focuses on identifying trends in an employee’s or vendor’s personal, professional, or company behavior that increases operational and security risk to an organization. Personnel security products are typically deployed as internet portals due to the extensive data mining requirements.
Examination at the network layer operates in-line with a network, discovering all assets in a network then identifying vulnerabilities in each asset. Network examination products can be delivered as an appliance, or as software running on a desktop or laptop. Automated appliances are the preferred method of deploying network-level examination.
Examination at the operating system layer provides detailed information about a host by discovering user accounts and fingerprinting the application and operating systems. A pre-defined rules set identifies the vulnerabilities. Examinations at the operating system level provide more in-depth information about a host than network-level examinations, and are typically deployed as “agents” on each host.
Application and database examinations focus specifically on vulnerabilities with a particular software application or database system. These products are written specifically for a certain software package or database. Examination products focused on software packages and databases provide the most basic level of security in a layered security model.
Detection
Detection products are reactive because they search for problems that already exist in a computing system. Detection products can be delivered in-line with a network, or at the firewall layer as “intrusion prevention” technology in which well-known attack signatures are used to detect intrusions before they enter a network.
The most common detection products available today focus on virus detection in email and intrusion detection at the network and host layer. Detection products are a necessary component of layered security; however, they are only effective when combined with proactive and preventive products in layered architecture.
Prevention
Prevention products focus on allowing or disallowing entry into a specific network or host. Such products can be as simple as access control lists in a router, or as advanced as “stateful” firewalls using sophisticated policies to evaluate and gate network traffic.
Firewalls at the network and host layer are common in all systems and use detailed information such as network addresses, host names, and services to evaluate whether traffic is allowed into a specific network. Network-based firewalls are an important security technology for any organization. Firewalls are the first line of defense in a network guarding against unauthorized intrusion.
Many plant control systems are part of a larger corporate network, separated and connected only by routers.
One of the first compartmentalization techniques used in a multisite organization is to implement a firewall at the edge of the plant network to increase intrasite security, while protecting intrusion from the corporate network and the internet.
Fig. 2 demonstrates placement of a single-site firewall to compartmentalize a plant network and secure against intrusions from other plants and the corporate network. Additional firewalls within a computing system can further secure critical layers within that system.
Encryption
Encryption products provide an additional layer of security by addressing data security both in transmission and storage. Encryption involves modifying readable text into a nonreadable state that requires technology to decrypt at the destination or delivery point.
Many encryption technologies such as VPNs focus on creating a secured transmission medium that prevents interception and deciphering of data during transmission. Other encryption products focus on securing stored data, both in databases and applications.
Encryption technology such as VPNs can be used in a plant control systems to provide secure remote access to critical assets. Specifically, Fig. 2 demonstrates how wireless remote control technology can be encrypted through a VPN to allow remote management of critical plant controls.
A wireless client incorporates VPN software to establish and transmit through a secured “tunnel” to the plant controls interface on the firewall. VPNs are highly recommended to secure either wire-based, or wireless access to critical assets from remote locations. ✦
References
1. MacLeod, D., and Whyte, D. “Towards System Survivability using the Single Virtual Enterprise Model and Layered Security through Information Protection Co-ordination Centres, A Position Paper,” Minister of National Defense, on behalf of Communications Security Establishment, Canada, 2000, p. 2.
2. Wells, M., and Thrower, W., “Defend Your Enterprise With Layered Security,” Symantec Advantage, Issue 11, Summer 2002, p. 1.
Nomenclature
Demilitarized zone (DMZ): A network used to separate computing assets that are exposed to public networks from internal computing assets.
Virtual private network (VPN): Technology that establishes a secured connection or “tunnel” over a network between two computing assets that supports secured and encrypted transmission.
Layered security: Deployment of security technologies in each layer of a computing environment to reduce the risk of unauthorized access by creating multiple points of resistance, and reducing the risk of failure from a single technology.
The author
Ken Miller ([email protected]) is a senior consultant with Ensuren Corp., Denver, which focuses on designing and implementing layered security solutions. He has 20 years’ experience in business and information technology, and has held numerous technical and management positions. Before Ensuren, Miller managed all engineering efforts at Circadence Corp. with direct responsibility for designing, implementing, and securing an Internet acceleration service for North America. He holds a BS from the University of Missouri, and an MS and MBA from Northern Arizona University.